Example flow for external users
The following diagram identifies the flow of authentication and authorization information for external users. Colors are used in the following ways:
- Orange - credentials information
- Blue - endpoint access information
- Green - resource access information
- Red - proxy user and session user information
Some values are used to determine multiple types of access. These values initially appear as black (when they do not apply to a single type of access), and then later appear in one or more specific colors (to reflect the value is being used at that point in the process for a specific type of access).
In the following example, an API call is triggered by Ray Newton, who is an external user, using a browser-based application.
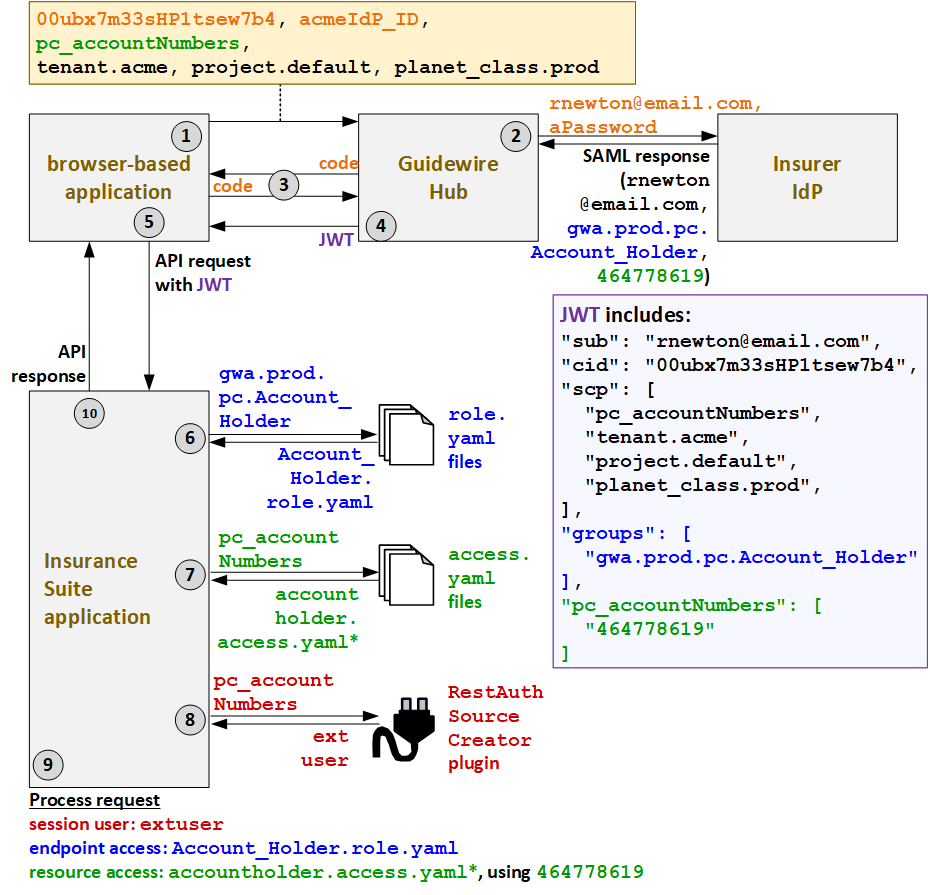
- When Ray triggers an API call, the caller application must first request a JWT from
Guidewire Hub. To initiate the process of getting the JWT, the caller application submits
its client ID (
00ubx7m33sHP1tsew7b4), the ID of the IdP (acmeIdP_ID), the application's resource access strategy (pc.username), and additional deployment information (tenant.acme,project.default,planet_class.prod). - To authenticate the user, Guidewire Hub acquires the user's user name
(
rnewton@email.com) and password (aPassword) through some type of login screen. It sends this information to the appropriate IdP. The IdP authenticates the user and provides a SAML response with the user's name (rnewton@email.com), the user's groups (gwa.prod.pc.Account_Holder), and the user's resource access IDs. For Ray, this is a list of his account numbers (464778619). - Guidewire Hub sends a code to the caller application. The caller application uses this code to request a JWT.
- Guidewire Hub generates a JWT and sends it to the caller application. This JWT includes
the client ID (
cid), ascptoken claim which names the resource access strategy (pc_accountNumbers) and additional deployment information, agroupstoken which names the user's groups (gwa.prod.pc.Account_Holder), and apc_accountNumberstoken which names the user's resource access IDs (464778619). - The caller application sends the API request to PolicyCenter along with the JWT.
- PolicyCenter determines the endpoint access. Based on the
groups listed in the JWT (
gwa.prod.pc.Account_Holder), theAccount_Holder.role.yamlAPI role file is used to define the endpoint access. - Next, PolicyCenter determines the resource access
strategy. Based on the resource access strategy value in the JWT
(
pc_accountNumbers), it grants resource access as defined in theaccountholderaccess.yamlfiles. (* PolicyCenter starts withaccountholder_ext-1.0.access.yaml, but this file references additionalaccess.yamlfiles whose name starts with "accountholder".) - To determine which proxy user to assign to the session, PolicyCenter calls the
RestAuthenticationSourceCreatorplugin. The JWT specified a resource access strategy ofpc_accountNumbers. So, the plugin returns the proxy user for external users:extuser. - PolicyCenter processes the request.
- The session user is the proxy external user:
extuser. - The endpoint access is defined by
Account_Holder.role.yaml. - The resource access is defined by
accountholderaccess.yamlusing the resource access ID of464778619.
- The session user is the proxy external user:
- PolicyCenter provides the response to the initial call.